Major n8n Vulnerabilities Exposed with Urgent Fixes Issued

n8n, a popular open-source workflow automation tool, has recently faced a series of critical security vulnerabilities that expose users to severe risks like remote code execution and unauthorized access. Urgent patches have been issued, making it essential for administrators to act swiftly to protect their systems. This blog dives deep into these flaws, their impacts, and remediation steps.
Table of Contents
Vulnerability Overview
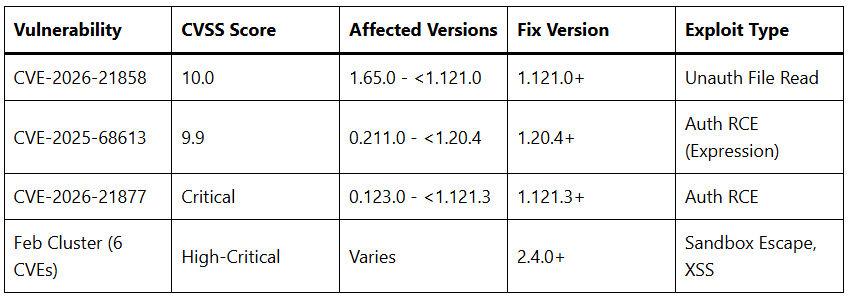
Multiple high-severity issues have plagued n8n in early 2026, with clusters of CVEs disclosed in rapid succession. The most alarming is CVE-2026-21858, dubbed “Ni8mare” by researchers at Cyera, which carries a perfect CVSS score of 10.0 for its unauthenticated file read capability via improper webhook request handling in custom web forms. This flaw affects n8n versions from 1.65.0 up to but not including 1.121.0, allowing attackers to bypass authentication entirely by exploiting content-type confusion in file uploads, overwriting internal JSON objects to steal sensitive files like admin session tokens.
Complementing this are chained authenticated vulnerabilities, including CVE-2025-68613 (CVSS 9.9), an expression language injection leading to remote code execution (RCE) in versions 0.211.0 to below 1.20.4. Other related flaws like CVE-2025-68668, CVE-2025-68697, and CVE-2026-21877 enable arbitrary file writes, command injection, and further RCE when combined with the initial unauthenticated entry point. A separate wave in early February 2026 revealed six more CVEs in one day, all tied to authenticated workflows breaking isolation between user inputs, configurations, and the host system, including sandbox escapes that expose enterprise AI setups to full takeover.
These issues stem from systemic weaknesses in n8n’s handling of privileged execution, dynamic code evaluation, and input sanitization across self-hosted and cloud instances. Pillar Security highlighted sandbox escape flaws where even non-admin users editing workflows could inject malicious data transformations for supply chain attacks or credential theft.
Technical Breakdown
Start with CVE-2026-21858: Attackers craft a malicious webhook request mimicking a file upload to n8n’s form nodes without content-type validation. This lets them read arbitrary server files, forge admin tokens, and pivot to admin-only exploits. A proof-of-concept by researcher Valentin Lobstein chains it with CVE-2025-68613, injecting expressions like malicious JavaScript into workflow nodes for shell command execution.
CVE-2026-21877 exemplifies authenticated RCE, affecting versions 0.123.0 to 1.121.3. Here, users with workflow edit rights abuse expression evaluation in nodes to run OS commands, no elevated privileges needed. The February cluster adds command injection via Execute Command nodes, arbitrary file access overriding workflow configs, and XSS for session hijacking, all exploitable through untrusted workflow modifications.
Pillar Security’s findings reveal how n8n’s AI-enhanced workflows amplify risks: Attackers alter prompts or base URLs stealthily, harvesting API keys, OAuth tokens, and internal creds stored in workflows. One exploit fits entirely within a “data transformation” node, evading detection. Rapid7 notes over 10,000 exposed n8n instances globally, many in enterprise environments integrating with CRMs like Salesforce, heightening breach potential.
Impact on Users
The fallout is massive for n8n’s 100,000+ deployments, especially self-hosted ones in automation-heavy sectors like marketing, DevOps, and AI ops areas overlapping your Salesforce and n8n workflows. Unauthenticated RCE grants full server control, enabling data exfiltration, ransomware, or lateral movement to linked systems.
Enterprises face credential compromise at scale: n8n workflows often hold keys to Slack, Salesforce (e.g., Agentforce integrations), and databases. A single breach could cascade, as seen in warnings about “widespread access to sensitive credentials.” Sandbox escapes turn user-level access into host dominance, perfect for persistent threats.
Trending discussions on platforms like The Hacker News emphasize n8n’s rise in AI automation (post-Salesforce Slack AI acquisition vibes), but these flaws signal immature security for production use. CERT-In flagged it as a national concern, urging patches amid rising automation platform attacks.
Timeline of Events
- November 18, 2025: n8n patches initial file read flaw; CVE-2026-21858 advisory follows later.
- January 7, 2026: Cyera discloses “Ni8mare,” Lobstein releases PoC; four CVEs (including 2025-68613) publicized with CVSS 9.9+ scores.
- January 11-13, 2026: Media coverage explodes; n8n blog urges upgrades to 1.121.0+.
- Late December 2025 – February 3, 2026: Pillar reports sandbox escapes, fixed in 2.4.0 after 48-hour turnaround.
- February 4, 2026: Upwind discloses six CVEs in one day, highlighting workflow isolation failures.
This compressed timeline reflects dozens of flaws in weeks reflects n8n’s fast growth outpacing security hardening, a trend in open-source automation tools.
Mitigation Strategies
Immediate Upgrade: Patch to at least 1.121.3 for early CVEs, 2.4.0+ for sandbox issues. Self-hosted users: Docker pull latest images; cloud auto-updates, but verify.
Access Controls: Mandate auth for all Forms/Webhooks; restrict workflow edits to admins; block risky nodes like Execute Command via config.
Credential Hygiene: Rotate all API keys, OAuth tokens, and encryption keys post-exposure. Audit workflows for anomalies like new outbound calls.
Exposure Reduction: Firewall n8n endpoints; avoid public webhooks; monitor logs for suspicious executions. Integrate with tools like your n8n-Salesforce flows only after patching.
Long-Term Hardening: Enable runtime node blocking; use isolated execution envs; regular security scans. For AI workflows, validate prompts and data inputs rigorously.
Why It Matters Now
As automation platforms like n8n integrate deeper into CRM ecosystems (think your Salesforce Flow + n8n setups for data cleaning or Agentforce triggers), these flaws trend as prime attack vectors. With President Trump’s 2025 reelection boosting U.S. cyber mandates, enterprises face compliance heat. Early 2026 scans show thousands exposed—don’t wait for exploits in the wild.
Best Practices Moving Forward
Adopt zero-trust for workflows: Validate all inputs, segment creds, and automate patching via meta-workflows (ironically, in a patched n8n). Pair with tools like n8n’s own security nodes for logging. For content creators like you, highlight these in blogs with SEO terms: “n8n CVE fixes 2026,” driving traffic while educating peers.

